Google Cloud Storage Prerequisites
Prerequisites
- By default, GCS authentication uses role-based access. You will need the data-syncing service's service account name available to grant access:
[email protected]
Step 1: Create a service account
- In the GCP console, navigate to the IAM & Admin menu, click into the Service Accounts tab, and click Create service account at the top of the menu.
- In the first step, name the service account that will be used to transfer data into Cloud Storage and click Create and Continue. Click Continue in the following optional step without assigning any roles.
- In the Grant users access to this service account step, within the Service account users role field, enter the provided Service account (see prerequisite) and click Done.
- Once successfully created, search for the created service account in the service accounts list, click the Service account name to view the details, and make a note of the email (note: this is a different email than the service's service account).
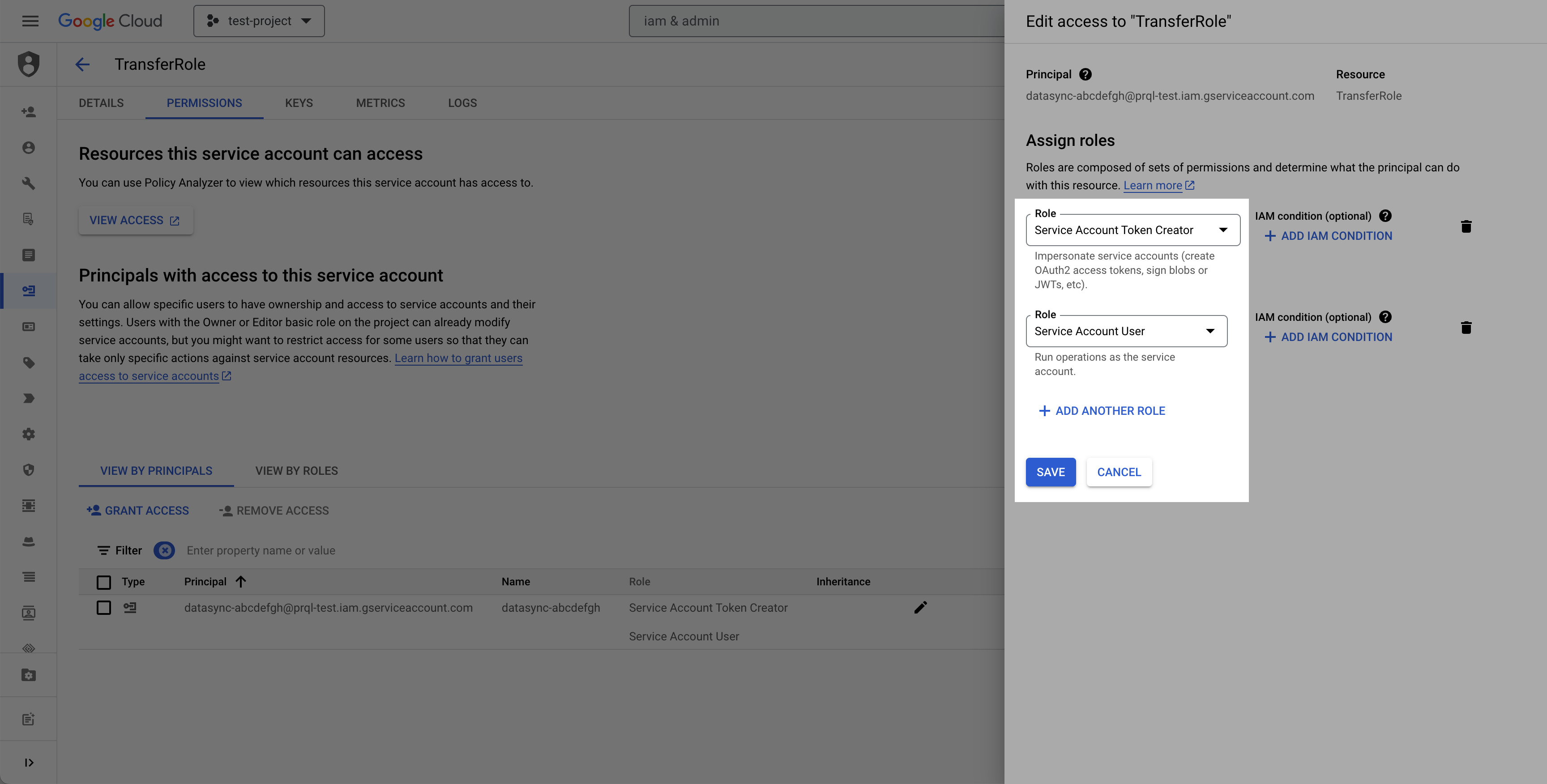
- Select the permissions tab, find the provided principal name (Service account from the prerequisite), click the Edit principal button (pencil icon), click Add another role, select the Service Account Token Creator role, and click Save.
Step 2: Create destination GCS bucket
- Navigate to the Cloud Storage page.
- Click Create.
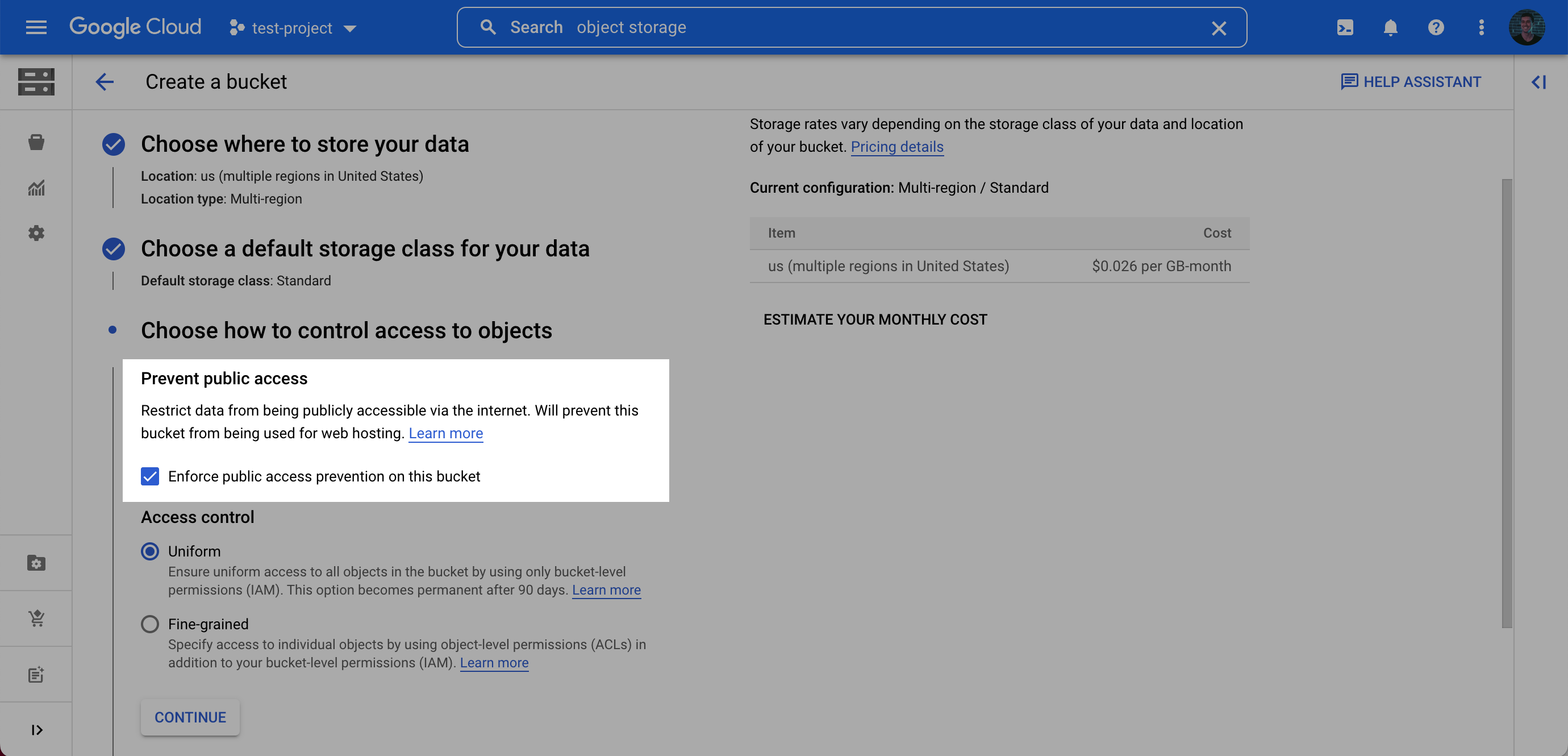
- Enter a bucket name, choose a region. Note: at the Choose how to control access to objects step, we recommend selecting Enforce public access prevention on this bucket.
- After choosing your preferences for the remaining steps, click Create.
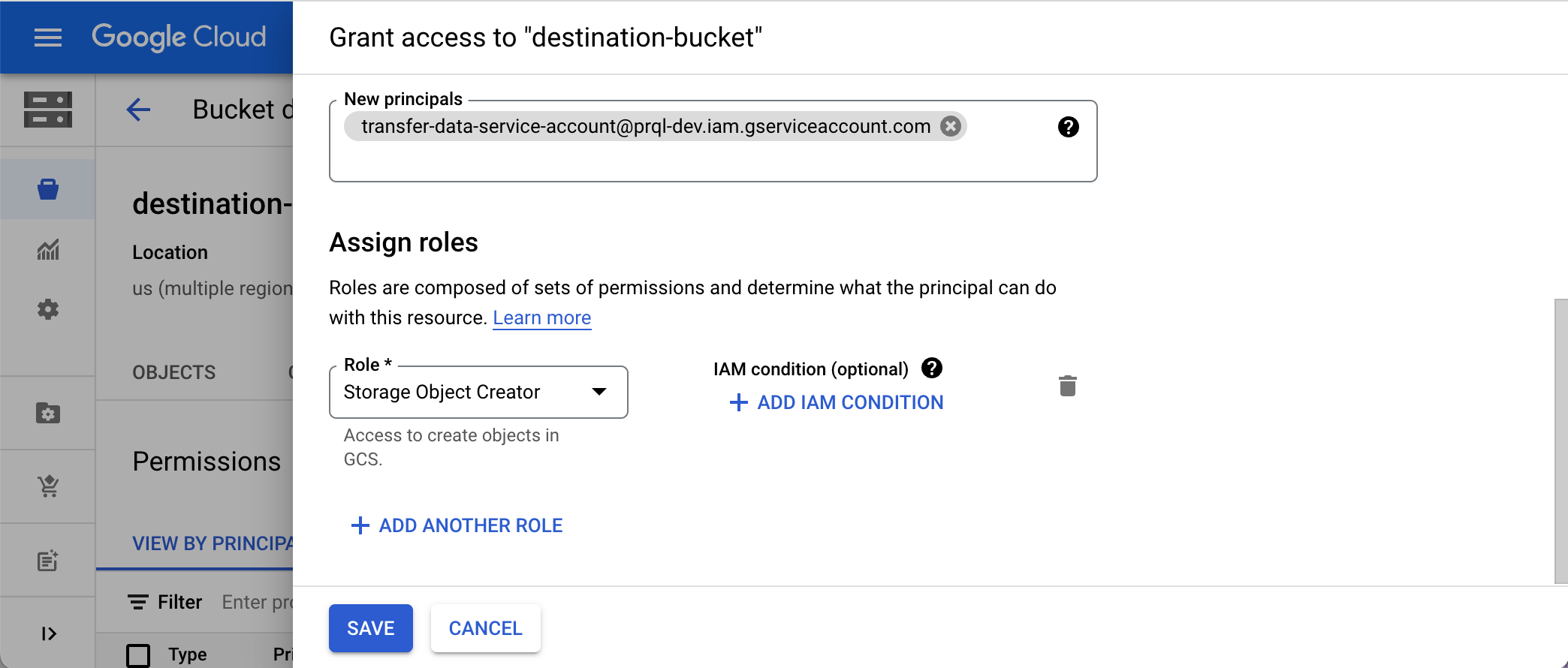
- On the Bucket details page for the bucket you created, select the Permissions tab, and click Grant access.
- Grant access to the principal (Service Account) you created in Step 1 (Note: this is the service account you created, not the service account from the prerequisite), and assign the Role: Storage Legacy Bucket Writer. Click Save.
Step 3: Gather the required setup information
For the data export setup, you will need:
- bucket name
- Your chosen bucket folder name
- Service account email
Visit the LogRocket Streaming Data Export settings page to complete the setup.
Updated over 1 year ago
What’s Next
Learn about how to configure the Streaming Data Export integration in app!
