Splunk
LogRocket offers two-way integrations with Splunk.
Add Splunk link within LogRocket
With our Splunk integration, you can jump directly from an issue in a network request on the frontend into your backend traces to help you uncover the root of an issue faster.
Visit the "Settings" page in LogRocket and click "Integrations". Scroll down to find the Splunk card and follow the instructions in-app to enable this integration.
Once enabled, you will see a link to Splunk from within a network request in LogRocket:
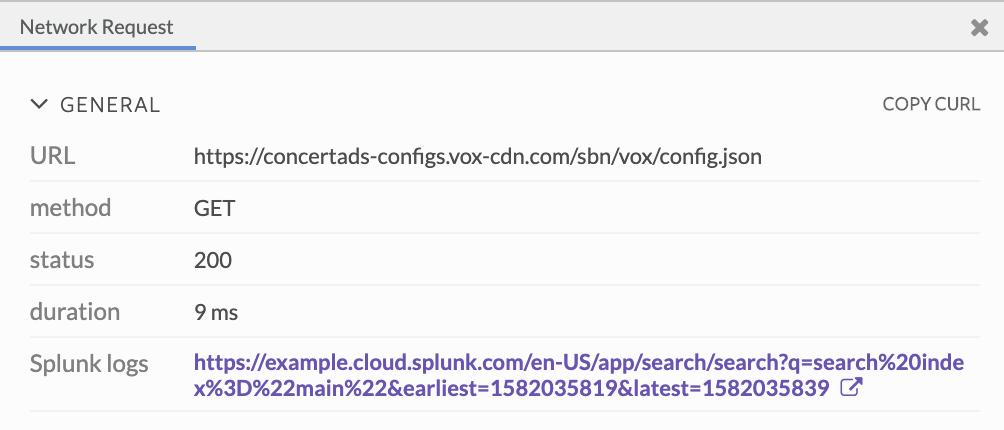
This links you to a list of relevant logs within Splunk, with search parameters matching the timeframe of the selected network request. You must be logged into Splunk to view the list.
Add custom parameters to Splunk query
In order to help you arrive more quickly at the relevant logs within Splunk, you can also choose to add custom parameters to your search query based on the network request.
The parameters you can select from are as follows:
| Parameter | Description |
|---|---|
request.url | The full requested URL |
request.method | The HTTP method of the request |
request.referrer | The request's referrer |
request.header.* | The full value of a request header (if present). E.g., to retrieve the value of the accept header, specify request.header.accept |
request.body.* | The full value of the specified body property in the request (only retrieves a value if the body is JSON and the property is present). E.g., to retrieve the value of a user property in the body, specify request.body.user (nested properties can be accessed as well) |
response.status | The HTTP status of the response |
response.header.* | The full value of a response header (if present). Behavior is identical to request headers above. |
response.body.* | The full value of the specified body property in the response (only retrieves a value if the body is JSON and the property is present). Behavior is identical to request body above. |
resource.mime_type | The MIME type of the resource. |
resource.initiator_type | The entity or element that triggered this request |
You can enter these within the Settings page for the integration.
If a particular variable is not available for a specific request, it will be ignored when constructing the Splunk query.
View LogRocket sessions from Splunk
In addition to jumping from LogRocket into Splunk, you can also go from your Splunk traces to a specific LogRocket session. Add the LogRocket session URL in a header to your API calls to backends which have Splunk set up:
var recordingURL;
LogRocket.getSessionURL(function(sessionURL) {
recordingURL = sessionURL;
});
// example API call
fetch(someAPICallhere, {
headers: {
// other headers
'X-LogRocket-URL': recordingURL,
},
});Splunk has a number of backend SDKs as well as a comprehensive REST API which all of them use. These SDKs will record the above header, allowing you to view the LogRocket URL for any tracked API call.
Updated 7 months ago
